今天抽空分析了一下这种说法的原理:
下面是一个典型SQL防注入程序的核心代码:
......
Url=LCase(Request.QueryString())
Ip=Request.ServerVariables("REMOTE_ADDR")
if instr(Url,"")<> 0 or instr(Url,";")<>0 or instr(Url,"where")<>0 or instr(Url,"select")<>0 or instr(Url,"chr")<>0 or instr(Url,"/")<>0 or instr(Url,"count")<>0 or instr(Url,"update")<>0 or instr(Url,"char")<>0 or instr(Url,"declare")<>0 or instr(Url,"master")<>0 or instr(Url,"mid")<>0 or instr(Url,"*")<>0 or instr(Url,"and")<>0 or instr(Url,"exec")<>0 or instr(Url,"insert")<>0 or instr(Url,"truncate")<>0 then
Flag=True
Set theRs=server.CreateObject("ADODB.recordset")
Sql="select * from hackrecord"
theRs.Open sql,theconn,2,3
theRs.AddNew
theRs("time")=cstr(now())
theRs("ip")=ip
theRs.Update
theRs.Close
set theRs=nothing
end if
......
程序过滤的很仔细,SQL注入的核心关键字都被检测了。
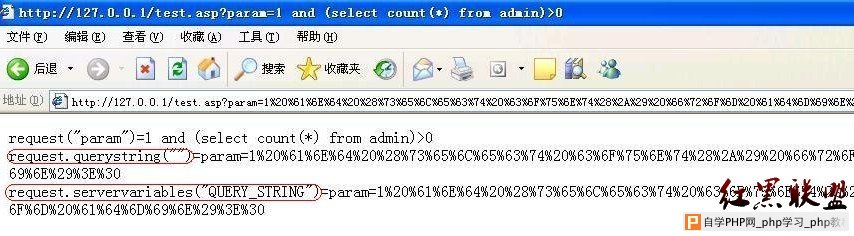
程序使用Request.QueryString来获取客户端提交的QUERY_STRING参数,下面是一个小实验,看过之后就不言而喻了。
test.asp文件
<%
response.write "request(""param"")=" & request("param") & "<br>"
request.querystring("")和request.servervariables("QUERY_STRING")是等效的
response.write "request.querystring()=" & request.querystring() & "<br>"
response.write "request.servervariables(""QUERY_STRING"")="& request.servervariables("QUERY_STRING") & "<br>"
%>
看如下浏览器截图(一目了然了):